LONDON — Sweetie looks much like other unfortunate young Filipinas. Just 10 years old, her user profile shows, she spends her days online fielding requests from men who offer her money to perform sexual acts in front of a webcam. When she logs on, invitations pour in – “Are you a working girl?” or “I’m into girls your age” – from strangers keen to get her into a private show via Skype or Yahoo! Messenger.
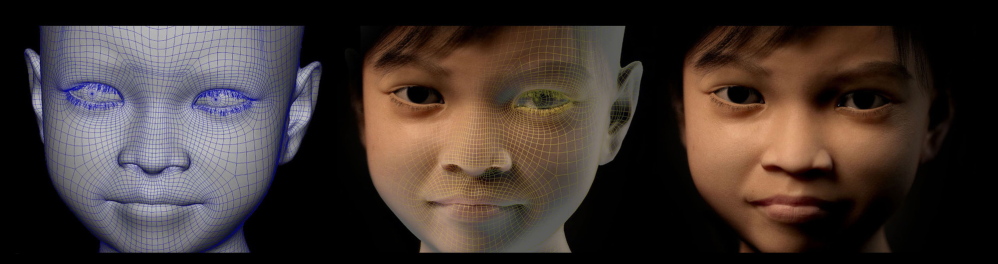
But Sweetie is actually a computer-generated avatar created by a Dutch nonprofit seeking to unmask sexual predators on the Internet.
Some 20,000 people contacted Sweetie during the eight weeks she was online last year, while researchers in an Amsterdam warehouse used keystrokes to turn her head, make her stare attentively or reach to adjust her webcam. After luring men in with the hyper-realistic animation, the group gathered e-mails, Facebook pages and head shots, then cut off contact before Sweetie engaged in sexual acts. It then gave dossiers on 1,000 suspects in scores of countries to Interpol.
SCARY TREND: ABUSE VIA WEBCAM
As the Internet makes it easier than ever for people to find and distribute child pornography, companies and organizations are creating technological tools to fight it. Microsoft has software that matches photos, even if they’ve been altered, so police can concentrate on new images surfacing online. Adobe Systems’ Photoshop helps identify victims with tools that sharpen pictures to unearth clues. Google blocks search terms related to child pornography.
“There’s limitless potential for technology to help solve the problem” of child pornography, said Mick Moran, head of Interpol’s Crimes Against Children unit in Lyon, France.
Pedophiles today find one another on Internet forums, peer-to-peer networks and hidden websites. The FBI estimates that 750,000 predators are online at any given moment. Victims, often found in chat rooms and on social networks, are becoming younger, and the abuse more violent.
Among the most worrisome trends is webcam misuse. As Internet access spreads in countries like the Philippines, Thailand and Sri Lanka, children as young as infants have been molested and raped on demand by family members and criminal groups for customers on the other side of the lens. Police in the Philippines say thousands of children have been victimized in this way.
In a rare crackdown on such abuse, authorities in Britain, the U.S. and Australia arrested 29 adults in January and identified 15 Filipino children in a case that began when recordings were found on the computer of a registered sex offender in England.
“It’s a new cottage industry,” said Hans Guyt, head of special projects at Terre des Hommes, the children’s rights group that created the Sweetie avatar with a local animation company that prefers to remain anonymous.
“It’s fueled by poverty at home and predators around the world with $100 to spare to watch a child get raped,” Guyt said in a cafe a few blocks from Amsterdam’s notorious red-light district.
Since 2002, the National Center for Missing and Exploited Children in Alexandria, Va., which analyzes photos flagged as potentially abusive, has reviewed 105 million child sex-abuse images – including 24 million last year, said Michelle Collins, head of the exploited children’s division. Tech companies must acknowledge their services can create havens for sex predators and they should take responsibility for helping control the problem, she said.
“Technology and industry and law enforcement are all important in this fight,” said Collins, who has worked at the group since 1998. “This isn’t a problem that’s going to be solved by arresting people.”
Among the tools used by the center is PhotoDNA, the Microsoft software that can identify versions of the same picture online by comparing so-called digital fingerprints, an analysis of various elements of an image that add up to a unique signature that doesn’t change even if the photo is edited. The program compares this fingerprint to a database of known child-porn images to determine if it’s new or has already been in circulation.
Microsoft donates PhotoDNA to law enforcement agencies and Collins’ organization. And the software giant uses it in-house to scan images stored on its SkyDrive service. When a photo is flagged, Microsoft locks the account and alerts police.
“Technology got us into trouble, and this suggests technology can help get us out,” said Hany Farid, a professor of computer science at Dartmouth College in New Hampshire who developed PhotoDNA with Microsoft. Farid says he can recall only one instance in which an image was misidentified as child pornography.
One of the biggest challenges is TOR, or The Onion Router, a network created by the U.S. Naval Research Lab a decade ago to provide anonymous communications to people in countries with authoritarian governments. Though TOR is still funded by the U.S. government, it harbors hundreds of illegal sites where you can hire a hitman, buy drugs, trade arms – or find child pornography. It’s almost impossible to track users because traffic on the network is routed through a system of 5,000 relays across the globe to mask identities.
Despite the difficulties of locating pedophiles on TOR, there have been some recent successes. On March 18, U.S. police announced the arrest of 14 men who operated a TOR porn site that had victimized more than 250 children. Posing as women, the men had courted young boys on social media sites to get them to expose themselves and abuse younger siblings and even animals.
Danish police in September 2012 uncovered child abuse images on TOR that, based on a few visual clues, they believed had come from the U.S. The Danes turned them over to Jim Cole, head of victim identification in the Cyber Crimes Center at the Immigration and Customs Enforcement in Fairfax, Va. A 20-year veteran of criminal investigations who has worked with the Army and the Department of Homeland Security, Cole was on an FBI-led task force and his specialty is tracking abusers using even the scantest information.
PHOTOSHOP TOOL CRACKS A CASE
“The Internet has emboldened people who earlier couldn’t knock on a neighbor’s door and say ‘Hey, I like child abuse material,’ ” said Cole. “We know where they are posting and where they congregate and we get involved when there is no IP address or e-mail. We show up when more traditional investigative methods don’t work.”
Among the images the Danes discovered was one of a toddler being abused on a bathroom counter. Using Photoshop to sharpen a blurry prescription bottle in the background, Cole found a name and the logo of the CVS Pharmacy chain. Another photo of a car interior was sent to contacts in Detroit who determined it was a 1998 Suzuki Samurai. A picture with a close-up of the suspect’s hand yielded a fingerprint.
The clues led Cole and his team to the suspect’s profile on Facebook, where they could identify victims from the man’s contacts. Police eventually located 15 children abused by Stephen Keating of Jesup, Ga. Last summer, Keating was sentenced to 110 years and ordered to pay $1.2 million in restitution to his victims.
Back at the warehouse in north Amsterdam, Terre des Hommes has dismantled the Sweetie operation. There’s no more black paper covering the windows. The hundreds of pictures of the sex predators have been removed from the walls. So have the printouts of conversations the men had with the 10-year-old avatar – snippets of chats like “I’m very badly horny” – that stand in stark contrast to screen shots from their Facebook pages of laughing family members, toddlers, a pregnant wife, an infant daughter.
“Our objective was to show how easy it is to identify these predators,” said Guyt. “And we exploded a hand grenade.”
Send questions/comments to the editors.



Success. Please wait for the page to reload. If the page does not reload within 5 seconds, please refresh the page.
Enter your email and password to access comments.
Hi, to comment on stories you must . This profile is in addition to your subscription and website login.
Already have a commenting profile? .
Invalid username/password.
Please check your email to confirm and complete your registration.
Only subscribers are eligible to post comments. Please subscribe or login first for digital access. Here’s why.
Use the form below to reset your password. When you've submitted your account email, we will send an email with a reset code.