HOUSTON — Turns out even former presidents can fall prey to hackers.
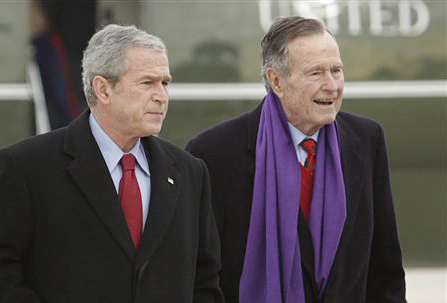
A mysterious email hacker apparently accessed private photos and messages sent between members of the Bush family, including both retired commanders in chief.
The Secret Service is investigating the breach, which appeared to yield little more than a few snapshots and some family discussions. But the incident illustrated how easily hackers can pry into private lives, even those of one of the nation’s most prominent and closely guarded political clans.
The Smoking Gun website displayed photos it said came from the hacker, including one that purported to show the elder Bush during his recent stay in a Houston hospital, where the 88-year-old spent almost two months undergoing treatment for complications from a bronchial infection.
The website said the hacker, who went by the online moniker “Guccifer,” gained access to the material through Bush family members and friends.
That could have made George W. Bush and George H.W. Bush vulnerable, even if they have the finest security that technology can provide. A friend or relative who clicked on a deceptive link or unwittingly downloaded a suspicious program might accidentally have exposed correspondence involving the former presidents.
“We can’t control what our friends do,” said Dan Wallach, manager of Rice University’s computer security lab and a computer science professor at the Houston school. “If my friends post a photo of me on Facebook, I can untag myself, but I can’t delete it. It’s not my photo. And that’s just a general-purpose problem.”
Reached by email, former Florida Gov. Jeb Bush called the hacking “outrageous.”
The rest of the family stayed quiet.
“There’s a criminal investigation and, as such, there’s nothing else we can say,” said Jim McGrath, a spokesman for George H.W. Bush in Houston.
Freddy Ford, a spokesman for George W. Bush, who has a home in Dallas, declined to comment.
Free email accounts from commercial providers are especially vulnerable to hackers who exploit easy-to-use features to reset email passwords. Many passwords can be reset by a hacker who discovers, for example, the birth year of a person’s mother, a father’s middle name or the name of a favorite pet.
That’s what happened to former Alaska Gov. Sarah Palin in 2008, when she was the Republican vice presidential candidate.
“That’s the first thing I thought of,” said Tyler Moore, an assistant professor of computer science at Southern Methodist University in Dallas. “The key here is when you’re famous or a well-known person or celebrity, there’s not a lot you can do if you’re targeted.”
A Tennessee college student named David Kernell was convicted two years later on federal charges.
Last year, Republican presidential candidate Mitt Romney’s free Microsoft Hotmail account was hacked after The Associated Press revealed that he and some top aides had used private email accounts to conduct state business at times when Romney was governor of Massachusetts.
The anonymous hacker claimed to have guessed the answer to a security question about Romney’s favorite pet to gain access to the account and change the password.
Email security is “a constant concern” in presidential politics, Romney senior adviser Eric Fehrnstrom said Friday.
“What we learned is that no matter how secure you make your system, there is someone out there spending every waking minute trying to subvert it,” he said.
Last year, a group of hackers known as the D33D Company published a list of what it said were usernames and passwords for more than 450,000 email accounts, including more than 25,000 AOL accounts. It was not immediately clear whether the Bush family’s hacked AOL accounts were among these.
On the Smoking Gun site, the word “Guccifer” was plastered across the photos in translucent, neon blue print. The site said “Guccifer” is a self-described veteran hacker who has long been in the government’s sights.
Whoever targeted the Bush family was probably not a “high-tech nation-state adversary,” Wallach said. “If it were, you wouldn’t see their tracks. … It’s probably somebody who thought they could make a quick buck.”
Unlike the email scams known as phishing that attempt to fool users into giving up bank account information and passwords, more sophisticated attempts called spear-phishing go after specific individuals or institutions, Wallach said.
According to the FBI, spear-phishing sends legitimate-looking emails that offer plausible explanations for requesting personal data, along with a link. Clicking on the link can download malware that gives the hacker access to things like address lists.
“It’s hard to know what kind of miscreant we’re dealing with here,” Moore said. “It could be someone trying to seek attention to show they can do it. You target a political figure, you’re trying to show, ‘Nobody is above what we can do.'”
Guccifer could be outside the U.S., making things more complicated for authorities in pursuit, Moore said.
“Of all the famous people to pick on,” he added. “I wouldn’t pick on someone who has an entire law enforcement branch dedicated to protecting them.”
Send questions/comments to the editors.


Success. Please wait for the page to reload. If the page does not reload within 5 seconds, please refresh the page.
Enter your email and password to access comments.
Hi, to comment on stories you must . This profile is in addition to your subscription and website login.
Already have a commenting profile? .
Invalid username/password.
Please check your email to confirm and complete your registration.
Only subscribers are eligible to post comments. Please subscribe or login first for digital access. Here’s why.
Use the form below to reset your password. When you've submitted your account email, we will send an email with a reset code.